Attention: Attack on the Ledger Connect Kit
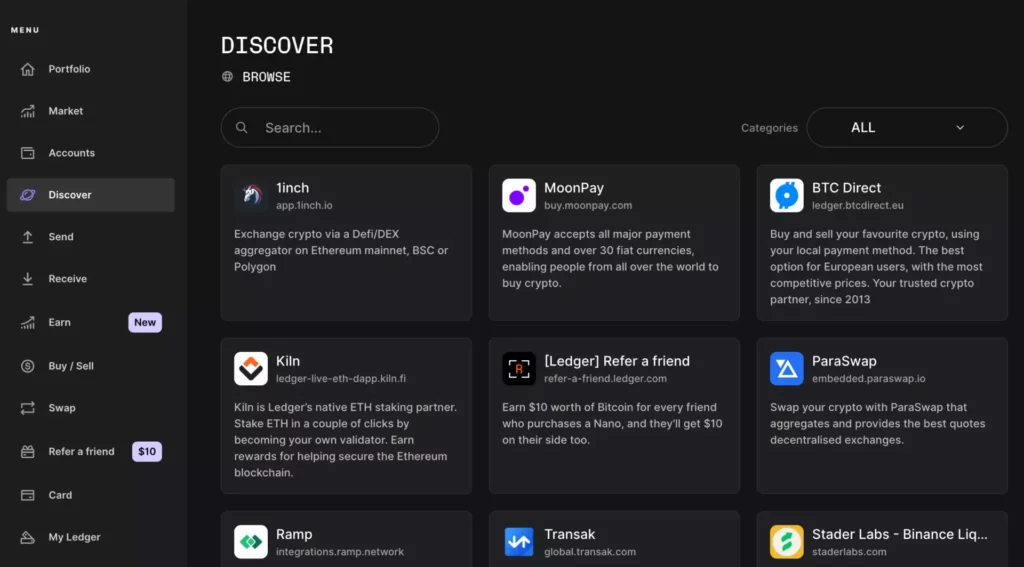
If you have a Ledger hardware wallet for cryptocurrencies, you should be careful: Ledger has warned its customers about a phishing attack affecting its Connect Kit. The Connect Kit is a software tool that allows you to interact with decentralized applications (dApps) using your ledger device.
What happened?
The phishing attack occurred on the morning of December 14, when a former Ledger employee was the victim of a phishing attack. The attacker gained access to his NPMJS account. NPMJS is a platform that provides JavaScript packages for developers. The attacker then released a malicious version of the Ledger Connect Kit (versions 1.1.5, 1.1.6, and 1.1.7 are affected). The malicious code used a fake WalletConnect project to redirect coins to a hacker wallet. WalletConnect is an open source protocol that facilitates communication between wallets and dApps.
What has Ledger done about the Ledger Connect Kit attack?
As soon as Ledger became aware of the problem, it reacted quickly and provided a solution within 40 minutes. The malicious file was active for about 5 hours, but Ledger believes that the window of time in which the funds were withdrawn was limited to less than two hours. With the help of WalletConnect, the fraudulent project was quickly deactivated.
A genuine and tested version of the Ledger Connect Kit (version 1.1.8) is now being distributed and is safe to use. Ledger has taken some security measures for developers working with the Ledger Connect Kit code. The development team of the Connect Kit in the NPM project is now read-only and cannot push the NPM package directly for security reasons. Ledger has rotated the secrets internally to publish them on Ledger’s GitHub. Developers are asked to check once again whether they are using the latest version, 1.1.8.
The attacker is now being sought
Together with WalletConnect and its partners, Ledger has reported the fraudster’s wallet address. The address is now visible on Chainalysis, a platform for blockchain analysis. Tether, a company that issues a stable cryptocurrency called USDT, has frozen the scammer’s USDT.
Ledger reminds its customers to always use Clear Signing with their Ledger device. Clear signing means that you check the transaction details on the screen of your ledger device before you sign them. What you see on the ledger screen is what you actually sign. If you still need to sign blindly, Ledger recommends using an additional Ledger Mint wallet or checking your transaction manually.
Ledger is actively talking to customers whose funds may have been affected and is proactively working to help these individuals. The lost funds will be reimbursed by Ledger. Ledger has pressed charges and is working with law enforcement authorities to find the attacker. Ledger is investigating the vulnerability to prevent further attacks.
Conclusion
Through a phishing attack on a former Ledger employee, a hacker was able to publish a malicious version of the Ledger Connect Kit. This made it possible to steal coins from users who used certain DApps via Ledger Live during a time window of around two hours on December 14. There was explicitly no attack on Ledger Live or the firmware of the hardware wallet. Those who do not use altcoins or DApps were not affected.

No Comments found