Secalot Review 2025
Secalot says it is an all-in-one digital security companion because it combines many functions. This also includes the option of using the stick as a hardware wallet. For this reason, I took a closer look at a copy that was kindly provided to me free of charge.
First Impression
Buy Secalot Online
Secalot can be purchased most easily and safely from the official webshop directly from the developer. There, the small stick currently costs (ERROR - no price), whereby shipping costs are calculated additionally. In addition to Bitcoin, credit cards and PayPal are also accepted as payment methods.
There are no official resellers in Germany yet, but the Secalot hardware wallet is also sold on amazon.
Hardware Wallets should preferably be ordered directly from the manufacturer or official resellers if possible. Dubious stores or private sellers on platforms like ebay or amazon could manipulate the devices for their own purposes or trick the buyer. This way, the thieves can steal all the coins from your hardware wallet at a later time. Unfortunately, there have already been such cases in the past.
Contents of the Package
Shipping to Germany went smoothly and took only three days. Depending on the selected shipping method, it is also possible to track his shipment. The envelope contains a small plastic bag with the Secalot hardware wallet. A label on the bag gives information about the version number and the date of manufacture.
The Secalot hardware wallet
The Secalot stick looks exactly like a conventional USB stick: it has a size of 60x15x10mm, weighs only a few grams and a cap protects the USB-A port.
There is no imprint, but two silver stripes on the front. behind which the two touch buttons are hidden. There is an eyelet at the end of the hardware wallet to carry the stick on your key ring or around your neck.
First Impression: Conclusion
Shipping when ordering from Secalot Shop is fast.
The scope of delivery is simple. A seal or other security measures that could make possible manipulations visible are not found here. Accessories such as a quick start guide or a note for the recovery seed are also not included.
Secalot itself looks like a simple USB stick. However, this is not necessarily a bad thing, since this sensitive security device is not immediately recognizable as such for everyone.
Setting up the Secalot hardware wallet
Never use a hardware wallet that is already set up. You must choose your own PIN code or password and do the backup yourself. This is not given by anyone!
Depending on which feature you want to use, different steps are required to set it up. In this review, the focus is of course on the use of cryptocurrencies.
Set up Bitcoin Wallet
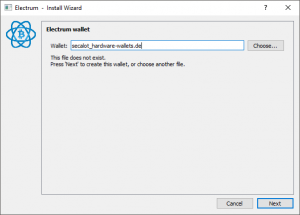
Bitcoin can only be used via a modified version of the Electrum software wallet. This can be downloaded from the Secalot download area. The initialization is started via the menu File > New Wallet.
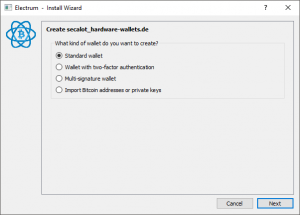
Here you first choose a name to distinguish Secalot Bitcoin Wallet from other wallets. In the next window, select the type of wallet. Normally, a standard wallet is sufficient, but it is also conceivable to set up a multisignature wallet, for example. Then you would need several wallets to sign a transaction, for example a TREZOR in addition to the Secalot hardware wallet.
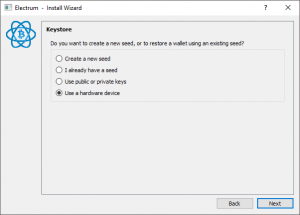
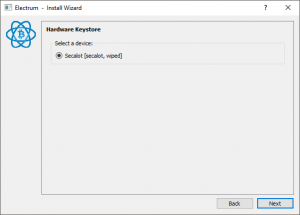
In the following window, select that the seed should be generated via a hardware wallet. Electrum then recognizes all connected hardware wallets, including Secalot.
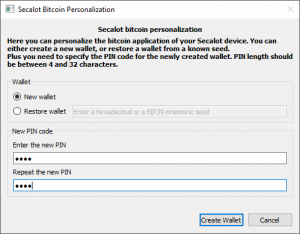
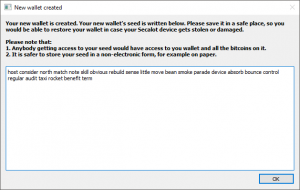
This is followed by the actual setup of the Secalot Bitcoin Wallet. You enter a PIN and Secalot generates a seed on the device. A backup of this seed is output in the form of 24 words.
Your Recovery Seed is the backup key to all your cryptocurrencies and apps. The Recovery Seed (backup) can only be viewed once. Never make a digital copy of the Recovery Seed and never upload it online. Keep the Recovery Seed in a safe place, ideally also safe from fire and water. Special backup products, for example Billfodl are suitable for this.
No one but yourself can be held liable for any financial losses caused by improper handling of sensitive data.
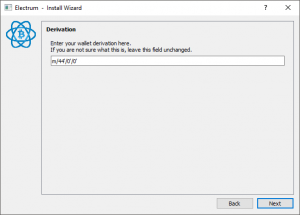
After that, experienced users can still change the derivation path, for example, to use Secalot as a SegWit wallet. In this case, the path would have to be changed from “m/44’/1’/0′” to “m/49’/1’/0”. The Bitcoin wallet is now ready for use.
Set up Ethereum Wallet
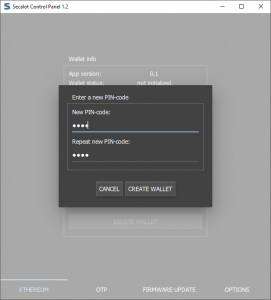
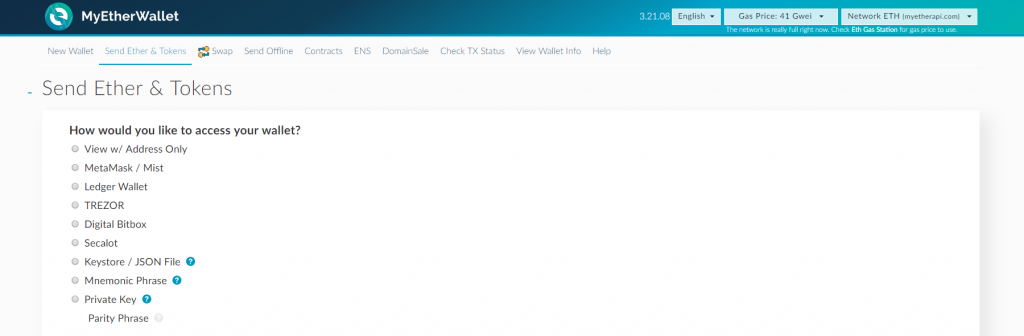
If you also want to use Ethereum with the Secalot hardware wallet, this is not possible via Electrum. For this purpose, the web wallet MyEtherWallet.com is used, whereby the wallet must be set up via the “Secalot Control Panel GUI”. These can also be downloaded from the Secalot download area.
On Windows, the application starts without installation and the Ethereum tab is opened directly. Here, in addition to a new wallet, an old one can also be restored. Then, just like Bitcoin, a PIN is chosen and then the recovery seed is noted. Secalot is now prepared for use via MyEtherWallet.com.
Secalot is also included in the list of available hardware wallets. If you select this, you will be prompted to enter the pin. Then, as with Bitcoin, you can choose the derivation path, after which the wallet opens.
Setup: Conclusion
Secalot completely forgoes its own software wallet and instead relies exclusively on third-party software such as Electrum or MyEtherWallet. As a result, there is no uniform and clear setup process as known from TREZOR or Ledger, for example. This could make it difficult for beginners and eventually lead to generating multiple seeds.
However, using the widely used and proven Electrum and MyEtherWallet wallets also has its advantages, as you have a wide range of functions at your fingertips without being dependent on the developers of the hardware wallet. I find it a pity that Secalot support is not integrated in the official version of Electrum, but a modified version of the developer has to be used.
Secalot handling
Managecryptocurrencies with Secalot
After the setup, Bitcoin as well as Ethereum and ERC-20 tokens can be managed via the software Electrum and MyEtherWallet. To do this, you use the corresponding software as usual. The only difference is that a transaction must be confirmed via the touch button.
All cryptographic keys are stored in the device and cannot be read. When a transaction is performed, the necessary information is passed to the device, Secalot signs the transaction and returns the signature.
Other Secalot security features
Secalot sees itself as a comprehensive security companion and therefore offers other features besides cryptocurrencies management.
Universal second factor (U2F)
With Secalot, it is possible to register one’s device with various services as a second secure factor, which must then be connected when logging into that service. So, for future logins, in addition to the normal login information, you still have to click the U2F touch button on the top of the device when prompted. Secalot supports simultaneous registration with an unlimited number of websites. Currently, for example, the following services support this standard: Google, Facebook, Dropbox, GitHub, GitLab, Bitbucket or also Nextcloud.
OpenPGP Smart Card
Secalot also behaves like a native smart card, allowing many different cryptographic actions to be performed. This opens up the possibility for a Secalot owner to integrate his device with a variety of existing software that uses GnuPG or a PKCS#11 interface. The following scenarios are thus conceivable:
- Email encryption and signing
- Computer login under Linux
- Hard disk encryption with the help of TrueCrypt
- File encryption and signing
- Establish VPN and SSH connections with the help of Secalot
Detailed instructions on how to set up the smart card can be found in the documentation: OpenPGP Smart Card.
One-Time-Password Generator (OTP)
OTPs can be used to securely log in to websites and applications such as password managers, and like U2F, act as a second factor. This type of generation is probably familiar to many from the Google Authenticator app. Instead of the app, you could now use a Secalot stick. By pressing both keys the one-time password is generated and typed directly into the field, because Secalot behaves like a keyboard in this case.
New services can be added via the “Secalot Control Panel GUI”. Since some OTPs require the current date, it is necessary to have a service running in the background.
Handling: Conclusion
This hardware wallet is very convenient to use in everyday life. No other accessories are needed to use the stick: Simply carry it on your keychain and plug it into a free USB port when needed. If everything is configured accordingly, the stick can now be used for secure communication and login, but also as a hardware wallet.
Supported Devices and Currencies
Secalot can be used on the following platforms:
The following cryptocurrencies are supported so far:
But Secalot is not just a simple hardware wallet. With many other functions, the stick is a real security all-rounder for everyday use. Because the following additional services are supported:
- Electrum
- MyEtherWallet
- SSH Agent
- OTP
- FIDO/U2F
- OpenPGP
- Password Generator
Documentation and Support
Secalot is still a relatively new one-man project. Nevertheless, there is an English documentation section that explains and describes all functions in detail. You can reach it via the official homepage: Secalot Documentation.
Support requests can only be made via a contact form.
Safety aspects
We are used to other hardware wallets attaching great importance to protecting the device from tampering attempts. For example, the devices are shipped with seals or the firmware is programmed to detect tampering and issue a warning. Secalot does not seem to have such provisions so far.
In addition, signing transactions with Secalot is somewhat riskier than with other hardware wallets. Because most of the others rely on their own display or at least have the option of pairing a smartphone. Thus, the information that is signed by pressing the touch button can also be displayed again beforehand. Otherwise, you could sign false data that has been manipulated during transmission. The recovery seed is also displayed here so that it cannot be read by viruses on the computer.
On the positive side, Secalot’s cryptocurrencies wallets are also protected from unauthorized use by a PIN. However, the entry here is made via the PC’s keyboard, which makes it possible to read out the PIN.
As befits a proper hardware wallet, the entire project is open source. Both hardware and software can be inspected for possible backdoors.
Product Specifications
| Advantages | |
| Disadvantages | |
| Compatibility | Electrum, MyEtherWallet, SSH Agent, OTP, FIDO/U2F, OpenPGP, Password Generator |
| Cryptocurrencies | Bitcoin, ERC-20 Tokens, Ethereum |
| Package Contents |
|
| Brand | Matvey Mukha |
| Platform | Windows, Linux, Mac |
| Altcoin Support | |
| Supported Coins | 3 |
| Open Source | |
| Secure Element | |
| Display as 2FA | |
| Interfaces | USB |
| Input Options | Touch buttons |
| Weight | 10g |
| Size | 60x15x10mm |
User Reviews get_comments_number($post->ID)
I just dug out my old Secalot unit and just can’t access it. This is the only page of info I can find on the internet. Your links are discontinued with just the Github page remaining. Any ideas how I can access my coins?









FAQ 0
Ask your own questionNo questions about the product available yet